
In ISO 27001 Roadmap – Part 3, we reviewed the Plan–Do–Check–Act (PDCA) model and how it aligns with ISO 27001.
Building on that foundation, this part focuses on how to move from planning into structured, control-driven implementation.
During the first part of the Planning phase, organisations establish the foundations of the ISMS. At a minimum, every organisation must address the following mandatory requirements:
Context of the Organisation (4.1–4.2): Identify internal and external issues, along with the needs and expectations of interested parties.
ISMS Scope (4.3): Define clear boundaries, including what is in scope and what is excluded.
Leadership Commitment and Information Security Policy (5.1–5.2): Secure top management endorsement and establish a high-level, strategic Information Security Policy. The ISMS is a strategic decision linked to the organisation's objectives, risk appetite, size, and operating model—this should be clearly reflected in leadership commitment and policy direction.
Roles & Responsibilities (5.3): Assign clear ownership and accountability for ISMS activities.
The second part of planning, which relates to risk management, can be more challenging, especially if you are implementing ISO 27001 for the first time. To avoid getting stuck, Cycubix's approach is to bring Annex A controls forward.
Annex A of ISO 27001 is a catalogue of information security control objectives and controls that must be considered during implementation. Annex A controls in ISO 27001 provide a structured set of measures used to treat identified information security risks.
The Annex A controls are grouped into four categories:
Although Annex A appears at the end of the standard, waiting until the end to review it often results in fragmented implementation and difficult mapping later.
By reviewing these controls early, organisations gain visibility into their current state. This facilitates:
✓ Identification of key information assets
✓ Identification of required policies and procedures
✓ Early identification of gaps in existing processes and controls
These controls are formally documented in the Statement of Applicability (SoA), which is one of ISO/IEC 27001's mandatory documented information requirements under Clause 6.1.3(d).
The SoA is a central reference that documents which of the standard's controls are relevant to the organisation's specific context, risks, and requirements.
It serves both as a planning tool (what will be implemented) and a formal justification of control selection.
The SoA is created after the risk management process has been completed, creating a tailored control framework for the organisation.
You may be wondering at this point how to connect the Controls from Annex A with the risk management process and the SoA. We will walk you through a structured process that transforms Annex A controls into a tailored, documented security framework captured in the Statement of Applicability.
Determining which controls are applicable requires a risk management process: the systematic application of policies, procedures, and practices to identify, analyse, evaluate, treat, monitor, and review risk.
At this stage, however, the focus is not on full risk evaluation, but on preparing for it in a disciplined and informed manner.
Unlike many ISO 27001 implementations that treat Annex A as a late-stage compliance exercise, Cycubix brings Annex A forward as an early discovery mechanism to guide risk identification, evidence planning, and documentation from the outset of the implementation.
✓ Accelerates compliance by clarifying exactly what needs to be built
✓ Identifies gaps before time is spent on unnecessary documentation
✓ Guides evidence collection with precision
✓ Ensures the ISMS addresses real, business-relevant risks
When used early, Annex A controls become a discovery tool. They help organisations survey their current state, identify information assets, and highlight areas where existing processes may be insufficient.
This avoids blind implementation—building controls before understanding whether they are relevant or already partially in place. At this stage, the goal is not yet to assess or treat risks in detail, but to determine which controls are relevant and what the organisation is missing, so that risk assessment can later be performed in a repeatable and efficient manner.
See available video resource to understand the process: A practical Six Step Approach to Drive ISMS Implementation
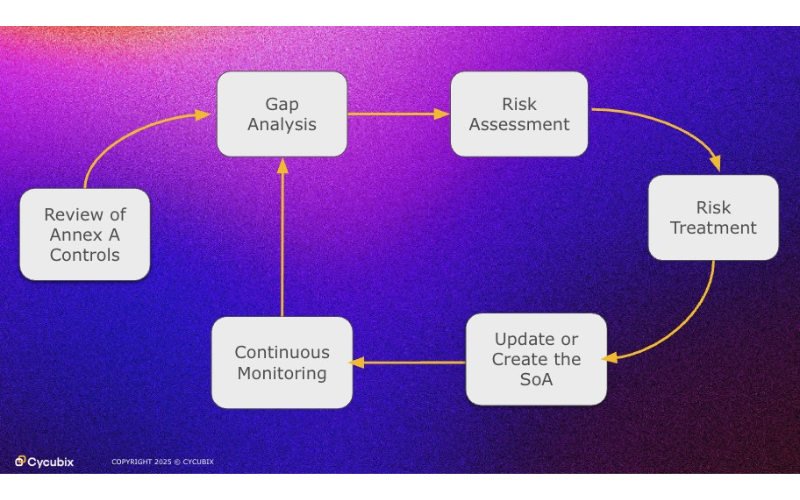
Using Annex A controls as an early input, the ISMS implementation follows a continuous, risk-based cycle:
The process begins with a thorough examination of the 93 controls listed in Annex A of ISO/IEC 27001:2022. The controls are organised into four themes: organisational, people, physical, and technological controls.
This initial review serves multiple purposes:
During this stage, organisations should consider each control in the context of their operations, industry requirements, and regulatory obligations. The goal isn't to implement every control, but to make informed decisions about which controls are relevant to their specific business requirements and strategic objectives.
With a solid understanding of Annex A controls, the next step is to assess the organisation’s current state. Gap analysis involves comparing existing security measures against the controls outlined in Annex A.
This honest evaluation reveals:
The gap analysis creates a clear picture of the current security posture and highlights the distance between where the organisation is and where it needs to be. This information becomes invaluable input for the risk assessment process that follows.
Risk assessment is the engine that drives control selection in ISO 27001. Rather than implementing controls arbitrarily, organisations use a structured methodology to identify, analyse, and evaluate information security risks.
This process examines:
The organisation's risk appetite and tolerance levels guide decisions about which risks are acceptable and which require treatment.
The risk assessment must be systematic, repeatable, and documented. It considers:
Once risks are identified and evaluated, the organisation decides how to address them. Risk treatment options include:
This is where the risk assessment directly informs control selection from Annex A. For each identified risk requiring treatment, the organisation selects appropriate controls that will reduce the risk to an acceptable level. Additional controls beyond Annex A may also be identified if needed to address specific organisational risks.
The risk treatment plan documents these decisions, assigning responsibilities, timelines, and resources for implementing selected controls. This plan becomes the foundation for continuously improving the ISMS.
The Statement of Applicability brings everything together into a single, comprehensive document. For each of the 93 Annex A controls, the SoA states whether it has been selected and provides justification for that decision.
For included controls, the SoA explains:
For excluded controls, the SoA documents:
The SoA is more than a compliance checkbox—it's a strategic document that demonstrates the organisation's thoughtful approach to information security. It shows auditors, stakeholders, and leadership that control selection is based on genuine risk considerations rather than arbitrary choices.
As the ISMS matures and circumstances change, the SoA is updated to reflect new controls implemented, changes in implementation status, or modifications to the control set based on evolving risks.
An ISMS is never truly finished. The final—and ongoing—stage of the cycle is monitoring and improvement.
This involves:
Internal audits, management reviews, and security metrics provide feedback on whether controls are working as intended. Incidents and near-misses offer learning opportunities. Changes in technology, regulations, or business operations may necessitate reassessing risks and updating controls.
This monitoring feeds back into the cycle, potentially triggering:
The cycle repeats, ensuring the ISMS remains dynamic and responsive.
Together, these six steps create an ISMS that is not only compliant but practical, auditable, and resilient. The cycle ensures that:
The continuous nature of the cycle prevents the ISMS from becoming a static set of documents that grow increasingly disconnected from reality. Instead, it remains a living framework that genuinely protects information assets while demonstrating due diligence to auditors, regulators, and customers.
Annex A controls should be reviewed early in the implementation process—not treated as a final compliance step. When used at the outset, they provide a structured way to identify information assets, highlight gaps in existing controls, and clarify what needs to be built or improved.
The Statement of Applicability then formalises these decisions, linking selected controls directly to the organisation’s risk assessment and business context. This ensures that control selection is not arbitrary, but grounded in real, justifiable risk-based decisions.
By anchoring the process in Annex A controls and the Statement of Applicability, organisations create clear traceability from identified risks through selected controls to documented decisions. This transparency makes audits smoother, security decisions more defensible, and the entire information security program aligned with business objectives.
In Part 5 of the ISO 27001 Roadmap, we will explore the information security risk management process defined in ISO/IEC 27005, covering risk identification, analysis, evaluation, treatment, acceptance, and continuous monitoring.
While ISO/IEC 27001 is the certifiable standard that requires organisations to perform risk management, ISO/IEC 27005 provides the structured methodology for how to do it effectively. By applying ISO/IEC 27005 in practice—supported by a well-structured Statement of Applicability (SoA)—organisations move beyond compliance-driven documentation toward a truly risk-based ISMS.
If you are structuring your implementation or preparing your Statement of Applicability, Cycubix can help you apply Annex A controls in a practical, risk-aligned way.
Reach out to the Cycubix team to explore our ISO 27001 consulting services.
Continue the ISO 27001 Roadmap >>>
Part 5: Upcoming!
Missed a step?
The ISO 27001 Roadmap series by Cycubix provides a step-by-step guide to building, implementing, and maintaining an Information Security Management System (ISMS), helping organisations worldwide turn ISO 27001 from theory into action.